Customize your Hack The Box Pwnbox
Setting up the environment persistence on Hack The Box Parrot Pwnbox

Currently working as a Senior Consultant at Netcompany spending my full-time job solving the SharePoint riddles. In the free time I'm expanding my understanding of cybersecurity through hacking activities. Git fanboy.
Introduction
Pwnbox is a customized, online Parrot Security Linux distribution - you can launch it from Hack The Box site and play with it in a browser (similar to the Kasm Workspaces streaming). It has immediate access to the HTB Challenges network, without additional VPN configuration.
More details: What is Pwnbox? How does it work?
Setup
I strongly recommend forking the repository then modify scripts to your liking. Disclaimer.
Collect and run init-pwnbox.sh script from my GitHub.
curl https://raw.githubusercontent.com/CyberEthicalMe/configs/master/htb-pwnbox/init-pwnbox.sh | sh
Explanation
Hack The Box is running user_init script each time Pwnbox is started. In the head of this file you can read.
#!/bin/bash
#This script is executed every time your instance is spawned.
So, I've put some effort creating the script that automates setting up the persistence on the Pwnbox by wgetting some resources and modifying the initial user_init script.
Details: init-pwnbox.sh
- Change current working directory to
$HOME/my_data. - Get preconfigured
user_initfile from the repository. Backups the original file. - Get Powerline font for
tmuxtheme (yes, I forced it a bit and I'm lovingtmuxnow). - Prepare
homedirectory to preload inuser_init. Things like.*.conffiles. - Create RSA keypair for persistence over SSH. It makes easier to come back to the server during the hacking challenges.
- Get terminal settings export script. This just saves the state of the default terminal (
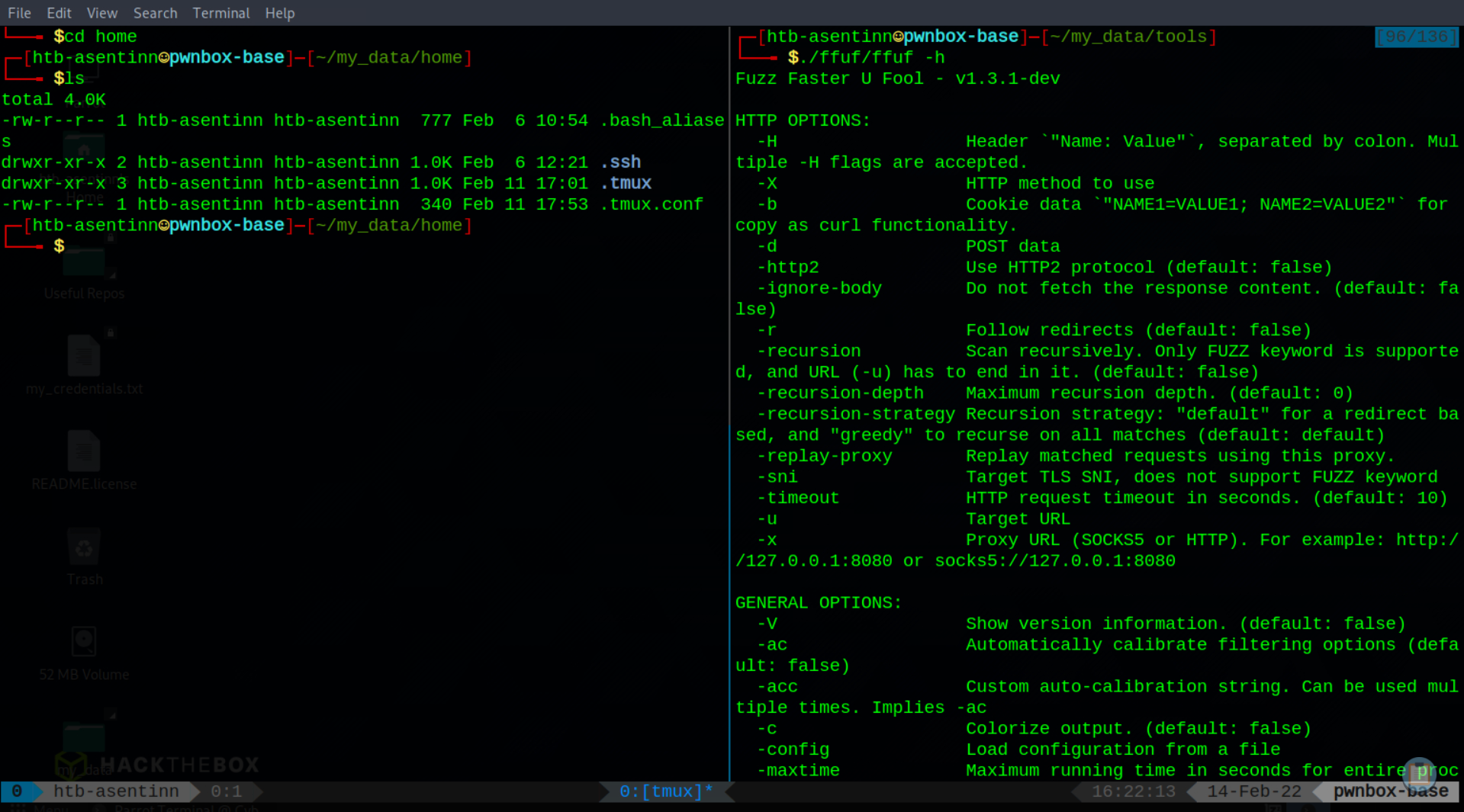
mate-terminal). - Clones tools repositories. Right now, only
ffuf, that is not available out-of-the box (pun intended). - Returns to the previous working directory.
Details: user_init
- Copy files from
~/my_data/hometo~. - Add Powerline font for
tmux. Refresh font cache. - Load
mate-terminalprofiles. May require manual switching profiles.
Known Improvement Points
- Manual refresh of
tmuxconfig (Ctrl+A, Shift+I) whentmuxlaunched for the first time. - Manual import of
mate-terminalprofiles. For some these are not imported on initialuser_init- use theimport-mate-terminal.shto import these on the first launch of terminal.




