Kali Linux on Amazon EC2
Attack Box via SSH

Currently working as a Senior Consultant at Netcompany spending my full-time job solving the SharePoint riddles. In the free time I'm expanding my understanding of cybersecurity through hacking activities. Git fanboy.
What will you learn?
- How to create Amazon EC2 instance
- How to secure your instance from unauthorized connections
- How to configure Kali Linux for your preferences in few minutes
At the end of this guide you will have a working Kali installation, accessible via SSH only for you.
Contents
- What will you learn?
- Create AWS account
- Create EC2 instance
- Connect to EC2 instance
- Kali configuration
- Conclusion
- Additional readings
Create AWS account
For this project, we are going to use the AWS EC2 instance within the AWS Free Tier account (it is more than enough).
Learn in details what is in scope of free license and what are its limitations on AWS Free Tier.
Creating the account:
During creation of the account, you will be asked to add a credit card (or payment provider) details. If you will be charged only when you exceed your Free Tier quota. Considering this, resources that AWS EC2 Free Tier has, are sufficient to run the instance continuously for a whole month.
Well, it depends on how you are using your EC2s, but I'm running there only single EC2 instance for this project. Just be careful with transfer - last month I was participating in Hack4Lem hackathon and next month I was charged $1.32 - not much for a ~2-3GB incoming data - but be warned.
Create EC2 instance
EC2 is an Amazon Elastic Compute Cloud. You can think about like a virtual machine in the cloud, that is managed by Amazon. This is an example of Infrastructure-as-a-Service (IaaS) because Amazon is responsible for managing hardware and networking, but users of EC2 are the ones responsible for OS, middleware, runtime, data and application.
Set data location
When you are logged in, the first things to do is to set a location, where your EC2 instance will be provisioned. This is done via a global setting that applies to all resources created in AWS (this can be changed later, of course)
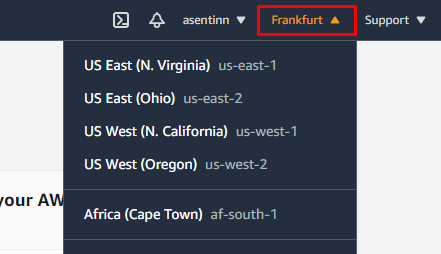
This project will be accessible only by me, so I'm choosing geolocation that is closest to my network provider - Frankfurt.
Configure instance
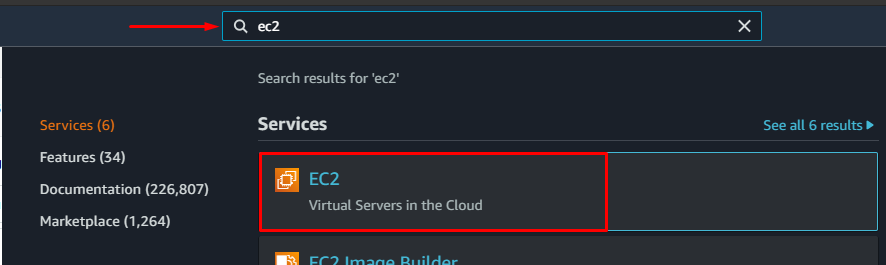
To create the EC2 instance, search "EC2" in the search bar on top of the portal and click it to navigate to the EC2 dashboard.
Now select Launch Instance and again in the dropdown.
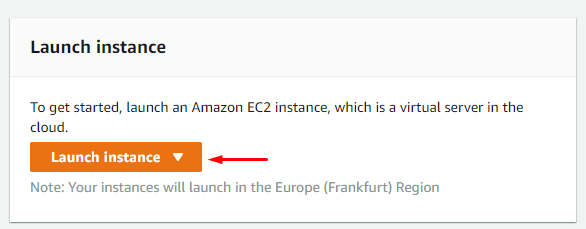
Notice that gray text reminds you about location of the instance that is being created
On this screen, search for latest Kali image and select it.
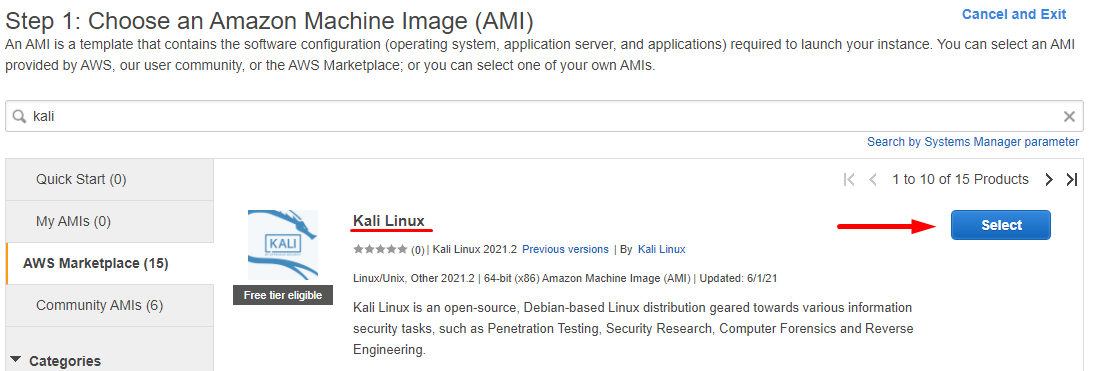
Rember to choose "Free tier eligible" when possible to avoid charges.
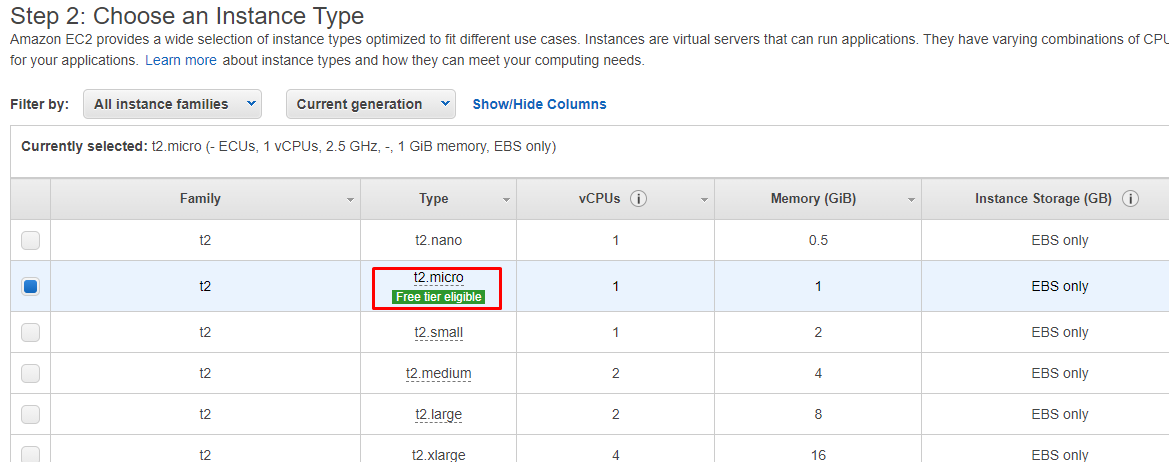
Ensure t2.micro is selected and click Next: Configure Instance Details.
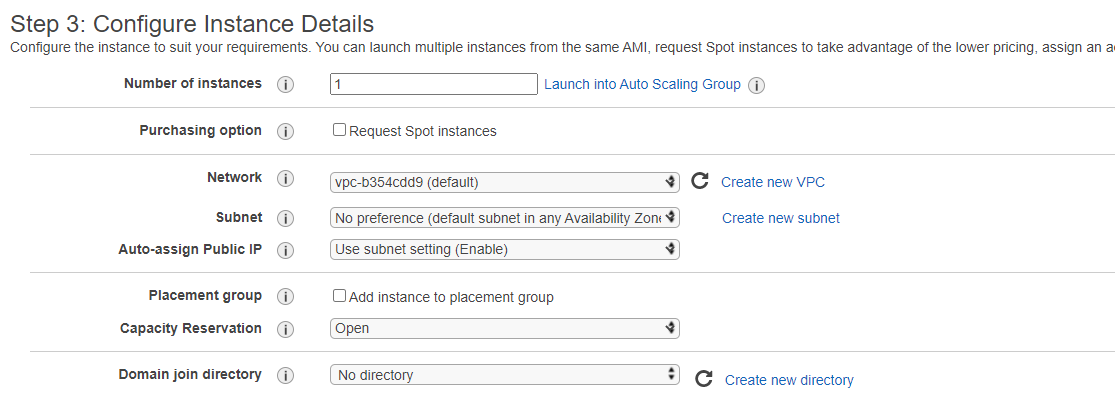
Leave defaults and click Next: Add Storage.
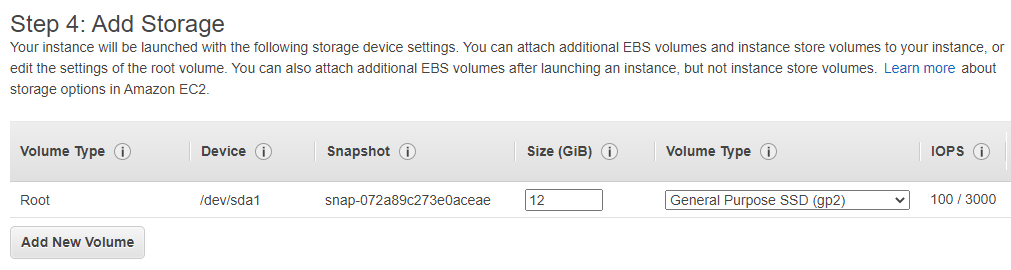
Leave defaults and click Next: Add Tags.
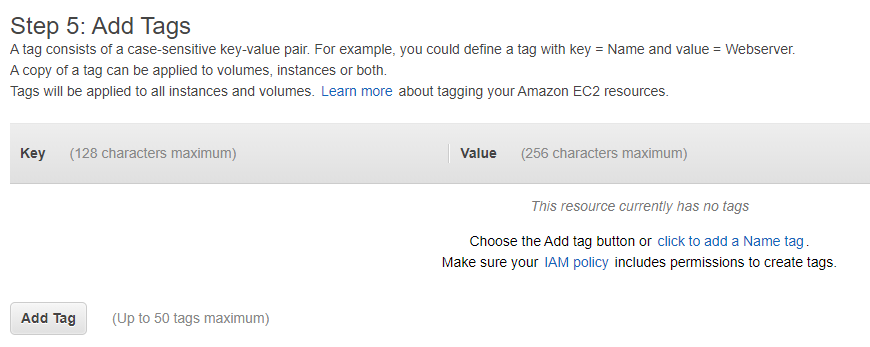
Here you can add some tags to help you identify for machine later - not a necessity in this project, but very useful in bigger setups. Click Next: Configure Security Group
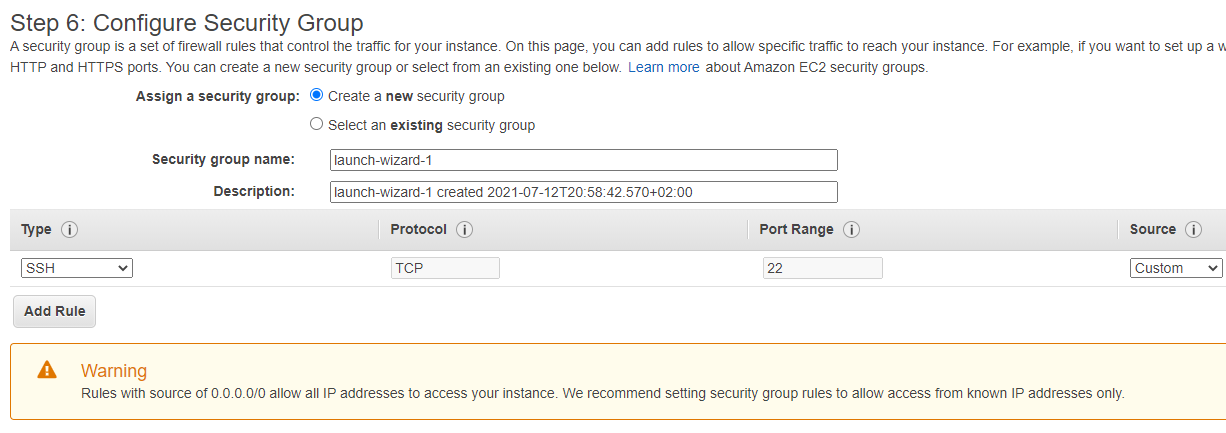
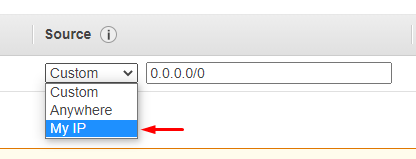
This is a crucial step, because of which we skipped the "Create and launch" button a few steps before. We are going to allow connections to the EC2 only to your IP. This is made by choosing "My IP" from the Source dropdown.
Because we need only SSH connection to the Attack Box only SSH have to be opened and configured as below.
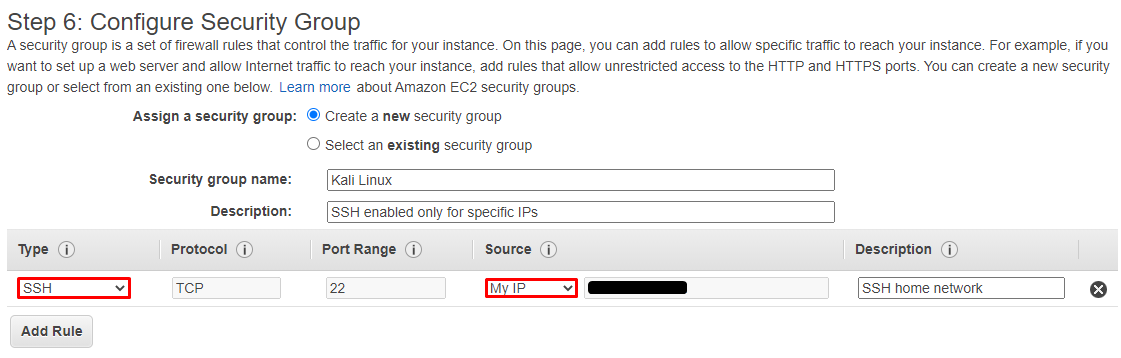
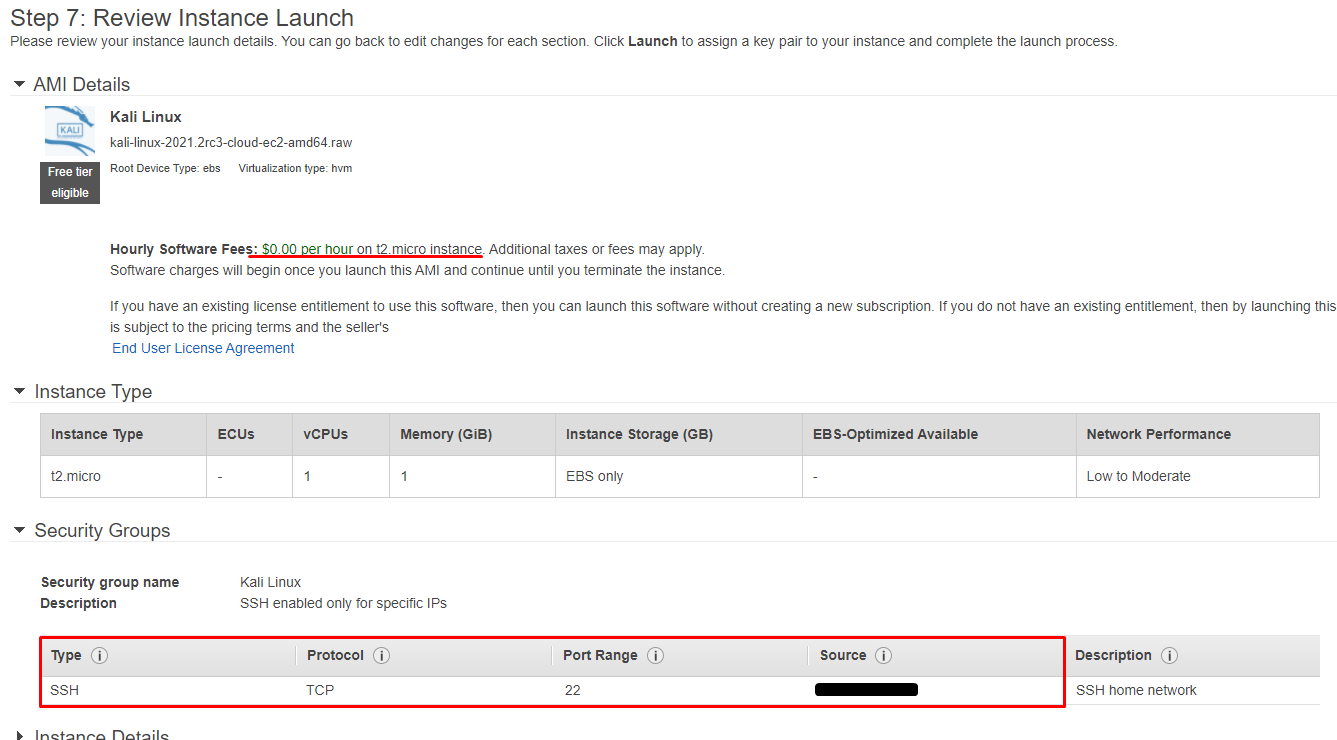
Go to the final step and make sure you have chosen "Free tier eligible" options and your access is configured only for your IP. Click Launch.
Before an instance is provisioned, you will be asked to choose/generate SSH key, so you can connect safely to your instance. Make sure you will store your private key safely. Think about it as a key to your house - you don't share it, you don't leave it in public spaces.
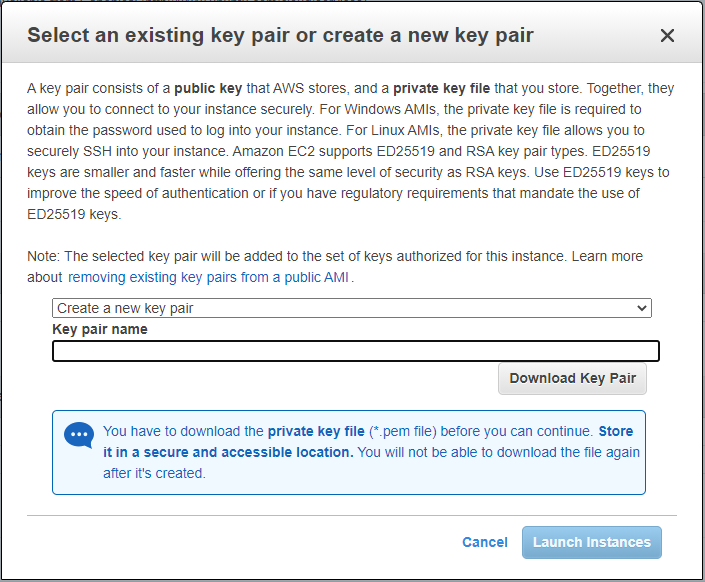
Finally, click Launch Instances and wait for you EC2 to be available.
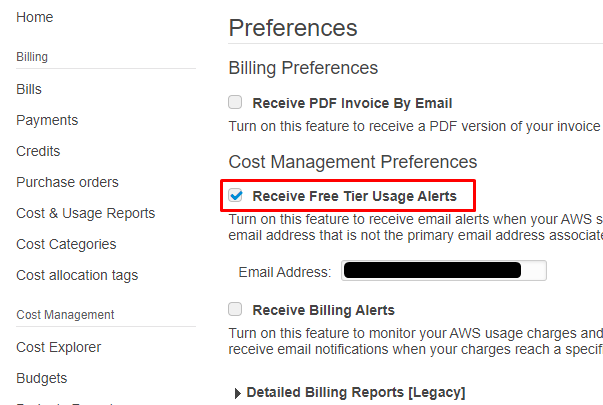
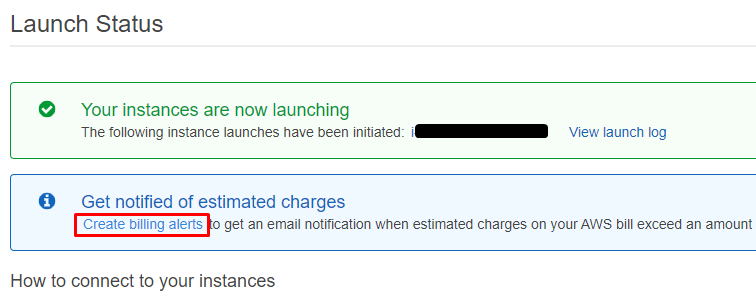
On final screen you can jump to billing preferences options and ensure that you have Receive Free Tier Usage Alerts option checked.
Connect to EC2 instance
🔔
CyberEthical.Meis maintained purely from your donations - consider one-time sponsoring with the Sponsor button or 🎁 become a Patron which also gives you some bonus perks.
To check if instance is ready to make connections, on the EC2 Dashboard select Instances
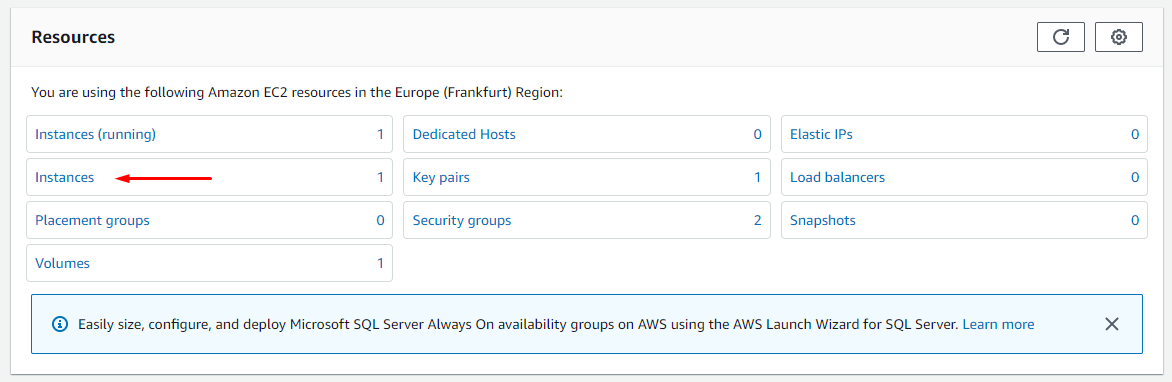
Here you should see that the instance is running and see its public IP. This is the IP you will be connecting to using SSH client.
It is possible to use one of the three other methods, but each of them requires installing some additional software on the box (like
ec2-instance-connect) and adidtional configuration. Becasuse we are going to use this Kali installation for pentesting and ethical hacking exercises, we should rely on secure SSH connection. Web browser managers poses more problems with shortcuts and response times and working via SSH is a great exercise for future challenges (my personal opinion). If you are still interested find this Set up EC2 Instance Connect Manual
You will be using the kali username, unless the other user is specified on the Kali's Default Credentials page.
Via Windows Subsystem for Linux
WSL comes with already SSH client preinstalled. So to connect to your EC2 instance, just type this command in command line
ssh -i <privatekey.pem> kali@<public IP>
If you don't have WSL configured on your system - there is no point to do such only to get SSH connection. This is where comes most widespread used SSH client. Putty.
Via PuTTY
Download both putty.exe and puttygen.exe from the download page.
Prepare private key
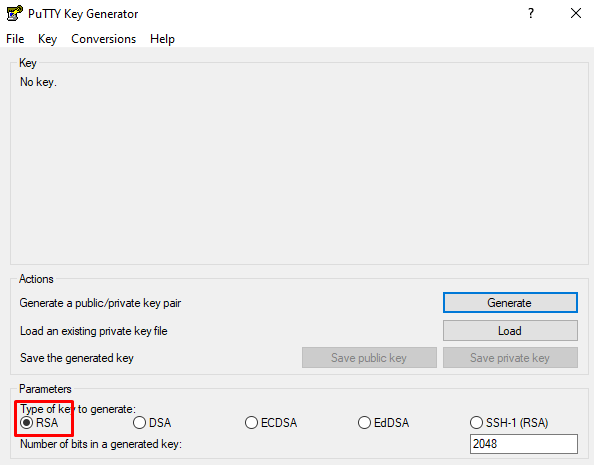
First we have to convert *.pem private key to *.ppk format supported by PuTTY. Run the puttygen.exe and make sure RSA is selected in the bottom panel.
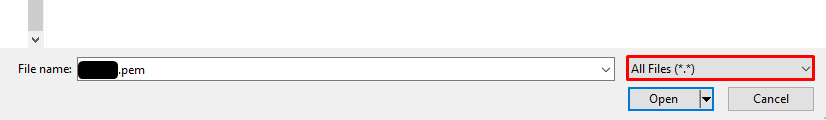
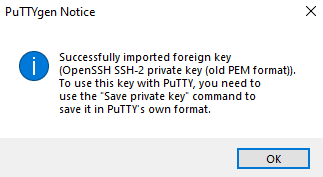
Then Load, switch to All files view and choose your private key.
You should see the following message
If you want to protect privae key with a password, fill the passphrase fields before going further
Click Save private key
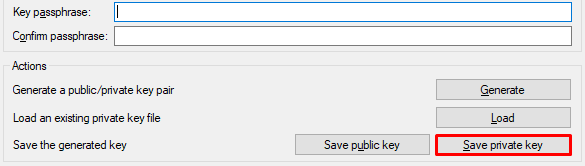
If you didn't enter the passphrase, ignore warning about saving private key without password
Choose a location for *.ppk file and save it. Now it is ready to use with PuTTY.
Connect to EC2 instance
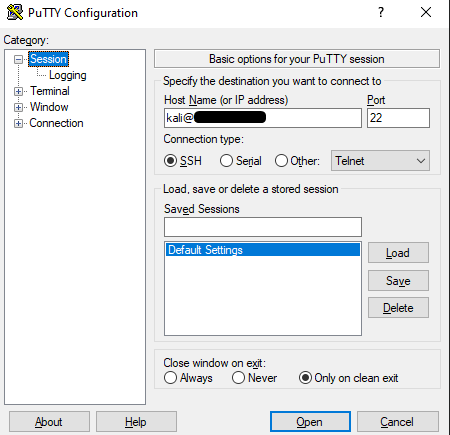
Launch PuTTY, enter in the Host Name the kali@<public IP> details of your EC2 instance, ensure port 22 and SSH is used.
Go to Connections settings and enter 600 seconds between keepalive signals.
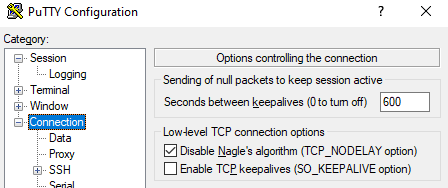
Defualt session timeout on the AWS is 20 minuts.
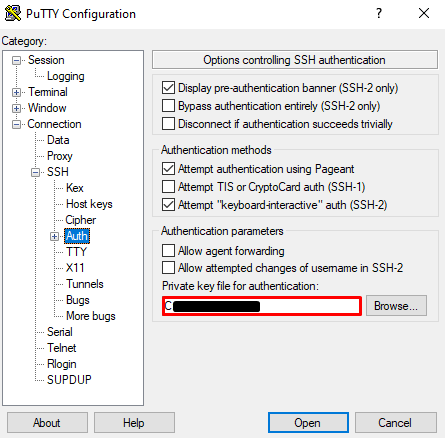
Go to Connections/SSH/Auth and choose *.ppk key to authenticate sessions.
Now to save these configuration details for later use, go back to Session, type name for the session and click Save.
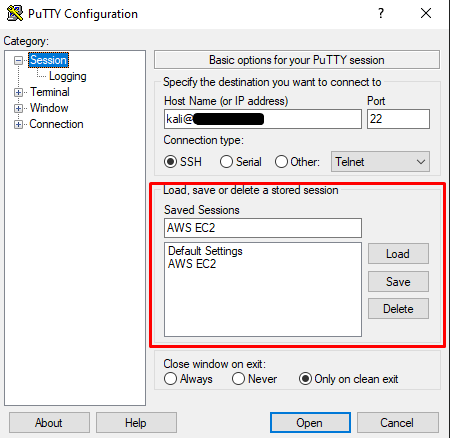
Now you can click Open.
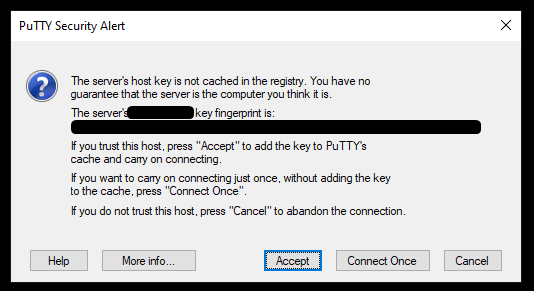
PuTTY console will open, and it will ask if you want to add the host to the trusted hosts. I am choosing Accept
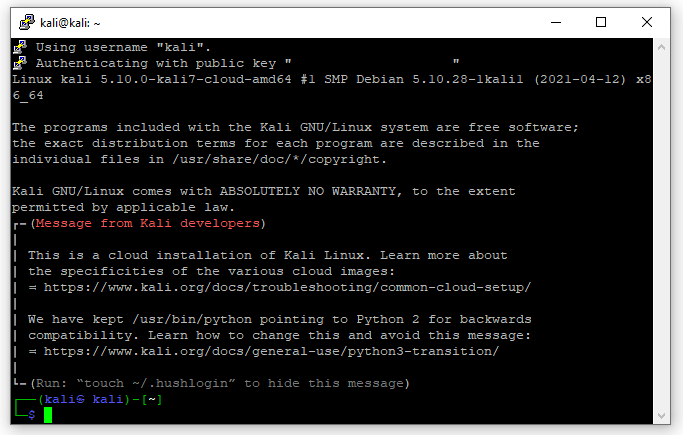
And that's it. If everything was done correctly, you should be welcomed by the Kali message and bash prompt.
Kali configuration
Update distro and packages
Paste the following instructions to update both system and packages.
sudo apt update &&
sudo apt dist-upgrade -y &&
sudo apt autoremove -y &&
sudo apt autoclean
You will probably be asked about adding users to kismet group. Add current kali user.
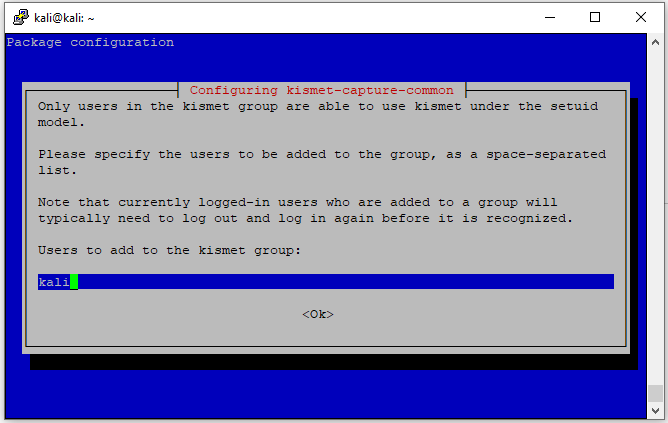
Kismet is an 802.11 layer-2 wireless network detector, sniffer, and intrusion detection system that comes preinstalled in Kali.
Hide welcome message
Hide it as was suggested in welcome message by creating .hushlogin file in profile
touch ~/.hushlogin
Resize font
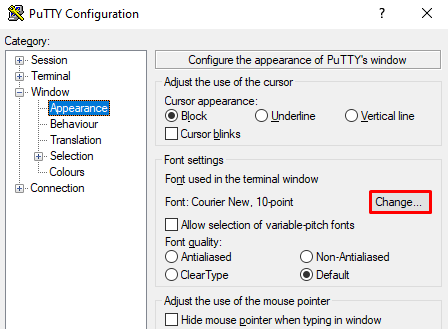
For me, default 10 points is definitely too small. This has to be changed in PuTTY before connection is made. So enter exit command and open PuTTY again. Load the saved session and go to Window/Appearance. In the Font settings/Change select desired size (I keep mine at 18), click OK and don't forget to save profile in Session/Saved Sessions/Save.
Now when connecting you should have bigger window and font.
Extend shell profile
Solution for this is posted by me on Unix StackExchange, but I'm copying here the quick version.
For this, we have to create new file in home directory, paste there your aliases, bindings, etc. Then reference that file in .zshrc.
Do not do this in
.bashrcbecause Kali since 2020.4 useszshinsteadbash. You can verify that by grepping/etc/passwd:$ cat /etc/passwd | grep kali
$ nano ~/.shell_aliases
Place here all you aliases and bash functions. You can take as an example, my .shell_aliases. Ctrl + S, Ctrl + X to save and exit.
Then edit .zshrc
$ nano ~/.zshrc
Paste this at the end of file
if [ -f ~/.shell_aliases ]; then
. ~/.shell_aliases
fi
Changes will be applied after session restart or immediately after
$ source ~/.zshrc
Bind word movement
This one took me a while to figure out, so I'm giving you my setup of you also have the issue with Ctrl + ←, Ctrl + →.
By default in any terminal and Windows Ctrl and arrow keys allow to navigate text by word. For my case, when I connect to Kali via PuTTY, it wasn't respected. I've searched through some topics at Stackoverflow, tried putting keybindings at different locations - and it didn't work.
If you have the same issue and advices found on the forums doesn't work, here is the solution.
First, get the ASCII codes for the mentioned key combinations. When showkey opens, type Ctrl + ←, Ctrl + → and ←, →. Note down each code.
$ showkey --ascii
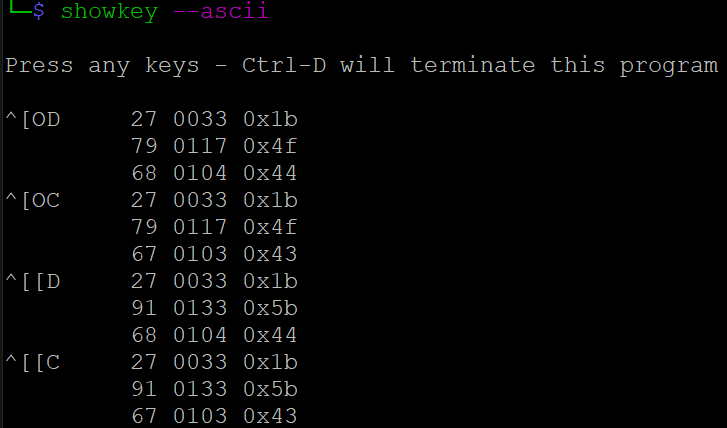
In my example
| Keystroke | ASCII Code |
| Ctrl + ← | ^[OD |
| Ctrl + → | ^[OC |
| ← | ^[[D |
| → | ^[[C |
Now, type the following in the .shell_aliases file created before
bindkey '^[OD' backward-word
bindkey '^[OC' forward-word
Recompile the profile by typing
$ source ~/.zshrc
Now try navigating word by word. Voilà!
Well, in my example by performing these action what happend is that hitting arrow key jums backward/forward by single word and Ctrl combination moves character by character. I still don't know how it happened. But remedy was using arrow ASCII codes for
bindkey(so opposite what you think should be).bindkey '^[[D' backward-word bindkey '^[[C' forward-word
Conclusion
Like what you see? Join the Hashnode.com now. Things that are awesome:
✔ Automatic GitHub Backup
✔ Write in Markdown
✔ Free domain mapping
✔ CDN hosted images
✔ Free in-built newsletter service
By using my link you can help me unlock the ambasador role, which cost you nothing and gives me some additional features to support my content creation mojo.
Now we have Kali installation working on remote - so accessible anywhere with connection to the Internet (as long as we config the IP address in the AWS Console).
You can find additional files to customize your Kali on my GitHub - for example, tools list that I'm using and shell installer.
Additional readings
📌 Follow the
#CyberEthicalhashtag on the social media🎁 Become a Patron and gain additional benefits
👉 Instagram: @cyber.ethical.me
👉 LinkedIn: Kamil Gierach-Pacanek
👉 Twitter: @cyberethical_me
👉 Facebook: @CyberEthicalMe